Trust Anchor in Raidiam Connect
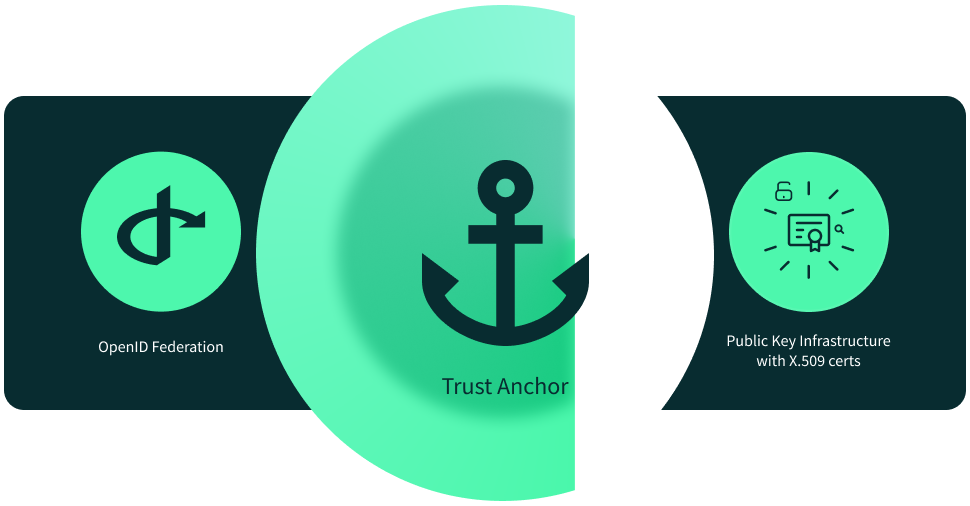
In Raidiam Connect, the Trust Anchor provides the infrastructure used to establish trust in a Trust Framework. You can use one of three trust models, based on your trust scheme:
-
OpenID Federation only
-
PKI/X.509 only
-
OpenID Federation + PKI/X.509 (hybrid)
Raidiam Connect’s trust infrastructure is built from two complementary components: the Participant Directory (the system of record for organisations and their technical resources) and the Trust Anchor (the mechanism used to establish and verify ecosystem trust).
In practice, the Directory holds the participant inventory and governance context, while the Trust Anchor issues/distributes/verifies the trust artifacts (for OpenID Federation, PKI/X.509, or a hybrid model) that participants rely on when exchanging data under a governance framework.
Trust models supported by Raidiam Connect
OpenID Federation only
Use OpenID Federation when your ecosystem trust model is based on signed metadata, federation entities, and trust chain resolution.
What Raidiam Connect provides
Raidiam Connect provides federation hierarchy management, participant onboarding for federation entities, federation policy controls, and trust chain resolution against agreed trust anchors. This enables participants to discover who they trust, verify that trust cryptographically, and apply consistent policy across the federation. It also supports ecosystem growth by allowing new participants and services to be onboarded without creating direct bilateral trust arrangements with every other participant.
Best fit for
This model is best for ecosystems that need dynamic trust discovery and policy-based validation between participants, especially where entities and technical metadata change frequently. It is particularly useful when operators want centralized governance with distributed trust verification, and when interoperability across multiple federation levels is a core requirement.
PKI/X.509 only
Use PKI/X.509 when ecosystem trust is established primarily through issued certificates and certificate validation.
What Raidiam Connect provides
Raidiam Connect provides Public Key Infrastructure services for certificate lifecycle management, key distribution, and certificate validation support. It gives operators a controlled certificate trust model with predictable issuance, rotation, and revocation processes. This model emphasizes strong cryptographic identity assurance for organizations and technical resources, certificate status, and operational key hygiene.
Best fit for
This model can be suitable for ecosystems that are certificate-centric and want to prioritize transport-level trust, strict PKI controls, and auditability. However, for larger ecosystems with many client applications and authorization servers, PKI-only designs can create higher operational overhead because client registration is usually handled via DCR rather than federation-native automated mechanisms.
If your ecosystem needs scalable onboarding and explicit trust-based client registration, Automated Registration in OpenID Federation is generally the stronger long-term model.
OpenID Federation + PKI/X.509 (hybrid)
Use the hybrid model when you need federation-based entity trust and PKI-based cryptographic trust at the same time.
What Raidiam Connect provides
Raidiam Connect combines OpenID Federation trust chain validation with PKI services for certificate-backed operations, including mTLS, certificate issuance and rotation, and key management. This gives ecosystems both metadata-driven trust decisions and certificate-based cryptographic assurance in a single operating model. In practice, this enables policy-driven participant trust at the federation layer while enforcing certificate-based controls for secure channels, client authentication, and key lifecycle operations.
Best fit for
This model is best for ecosystems that require both federation metadata trust and certificate-based security controls, often with centralized trust decisions via a Trust Registry and modern security profiles.
It is typically chosen when ecosystem governance needs to scale across many participants while still meeting strict technical security and assurance requirements for production data exchange.