OpenID Federation in Raidiam Connect: trust anchor and intermediate models
Raidiam Connect implements OpenID Federation trust anchor capabilities so you can build and operate production trust ecosystems, including intermediate trust anchor models, without custom federation infrastructure.
This page focuses on how federation works in Raidiam Connect. For protocol concepts and specification details, see the OpenID Federation concept pages.
Choose your OpenID Federation operating model
Single OpenID Federation
Use Raidiam Connect as the trust anchor for a single ecosystem, where all organisations and technical resources are managed within one federation scope derived from the Participant Directory. This is a good fit when you have one governance authority and rulebook, and want one canonical place to onboard participants and publish consistent, governance-aligned federation metadata (controlled by role and domain context).
Example use case
A country-level Open Finance scheme (or a private multi-bank data-sharing network) where all participants must be discoverable under one trust anchor and follow one registration and security profile.
How single federation trust works in practice
Participants onboard their organisations and technical resources (apps, authorization servers/OPs, resource servers), receive unique entity identifiers, and then other participants can discover metadata and validate trust relationships by resolving the trust chain anchored in the agreed trust anchor using the federation endpoints exposed by Raidiam Connect.
Federation of federations
Use this model when you need a shared top-level trust model across multiple domains (e.g., jurisdictions, business networks, or sector schemes), while allowing each sub-federation to manage its own participants and operational governance.
Raidiam Connect can operate the root trust anchor and/or one or more intermediate trust anchors, and other sub-federations can be rooted in a trust anchor from any provider—participants still validate trust via the agreed federation authorities in the trust chain.
Example use case
A “Global Open Finance Federation” defines common baseline policies and interoperability requirements, while regional schemes (Europe, LATAM) and national schemes (UK, Brazil) onboard and govern participants locally.
How federation-of-federations trust works in practice
Each sub-federation onboards organisations and technical resources into its own scope (via its directory-backed model), issuing metadata that’s governance-aligned to that domain.
Cross-federation trust is achieved by chaining trust from the sub-federation up to the root (or a trusted superior) authority, using federation endpoints for trust operations, discovery, and metadata retrieval.
Raidiam Connect as an Intermediate Trust Anchor
Use this model when a federation is ultimately rooted in another provider/authority, but you want Raidiam Connect to operate a sub-federation (e.g., for a country/region/sector) with its own onboarding, metadata publication, and day-to-day governance controls. Participants in that sub-federation still resolve and validate a trust chain that leads to the agreed root authority, while relying on Raidiam Connect’s federation endpoints for trust operations, discovery, and metadata retrieval within the delegated scope.
Example use case
A regulator-operated national root federation delegates sector-specific onboarding (e.g., “Open Insurance”) to an industry body that runs Raidiam Connect as an intermediate trust anchor.
How intermediate trust anchor operations work in practice
Organisations and technical resources are onboarded into the delegated scope (directory-backed), represented as federation entities with unique entity identifiers, and metadata issuance can be controlled by role and domain to stay aligned with local governance.
Example use cases for OpenID Federation with Raidiam
Open Data ecosystems (Open Finance, Health, Energy, and more)
OpenID Federation helps operators run Open Data ecosystems with consistent participant onboarding, policy-driven metadata publication, and verifiable trust across organisations and technical resources.
To see how to set up the trust framework and onboard participants, start with Getting started with setting up trust framework for open private ecosystem and Participate in open data ecosystem.
For domain examples across Open Finance, Open Insurance, Open Health, and energy-style multi-domain trust, see OpenID Federation – The Missing Link for Scalable Trust in Data, AI, and Wallet Ecosystems.
Agentic AI access control
OpenID Federation provides a structured trust model for AI agents and APIs. AI agents (or the services that run them) publish signed metadata, and APIs and authorization servers validate trust chains and policy constraints before allowing access or issuing tokens.
For implementation detail and architecture patterns, see Building Access Control for Agentic AI with OpenID Federation and Securing Agentic AI Access: Trust, Identity, and Authentication.
Wallet ecosystems
In wallet ecosystems, OpenID Federation supports trusted discovery and interoperability between issuers, wallets, and verifiers by anchoring participants in a common trust framework.
For implementation guidance, see Getting started with wallet ecosystems and Creating wallet ecosystems.
For broader trust architecture context across wallets and federated governance, see OpenID Federation – The Missing Link for Scalable Trust in Data, AI, and Wallet Ecosystems.
How federation is operated in Raidiam Connect
When you define federation as the trust model for an ecosystem, federation scope is derived from the Participant Directory. That includes all onboarded organisations and their registered technical resources within that ecosystem.
Participant onboarding and governance
Federation operators and/or participants onboard organisations, applications, authorization servers, identity providers, and resource servers within the federation scope derived from the Participant Directory.
Governance policies define who can onboard each resource type, what accreditation and role/domain checks are required, and how metadata is issued for each onboarded entity. Each onboarded technical resource can be represented as a federation entity with a unique entity identifier.
Federation, authorities, and domain/role mapping
In Raidiam Connect, you can attach Authorities to a federation. An authority is a key participant that accredits organisations and assigns Domains and Roles.
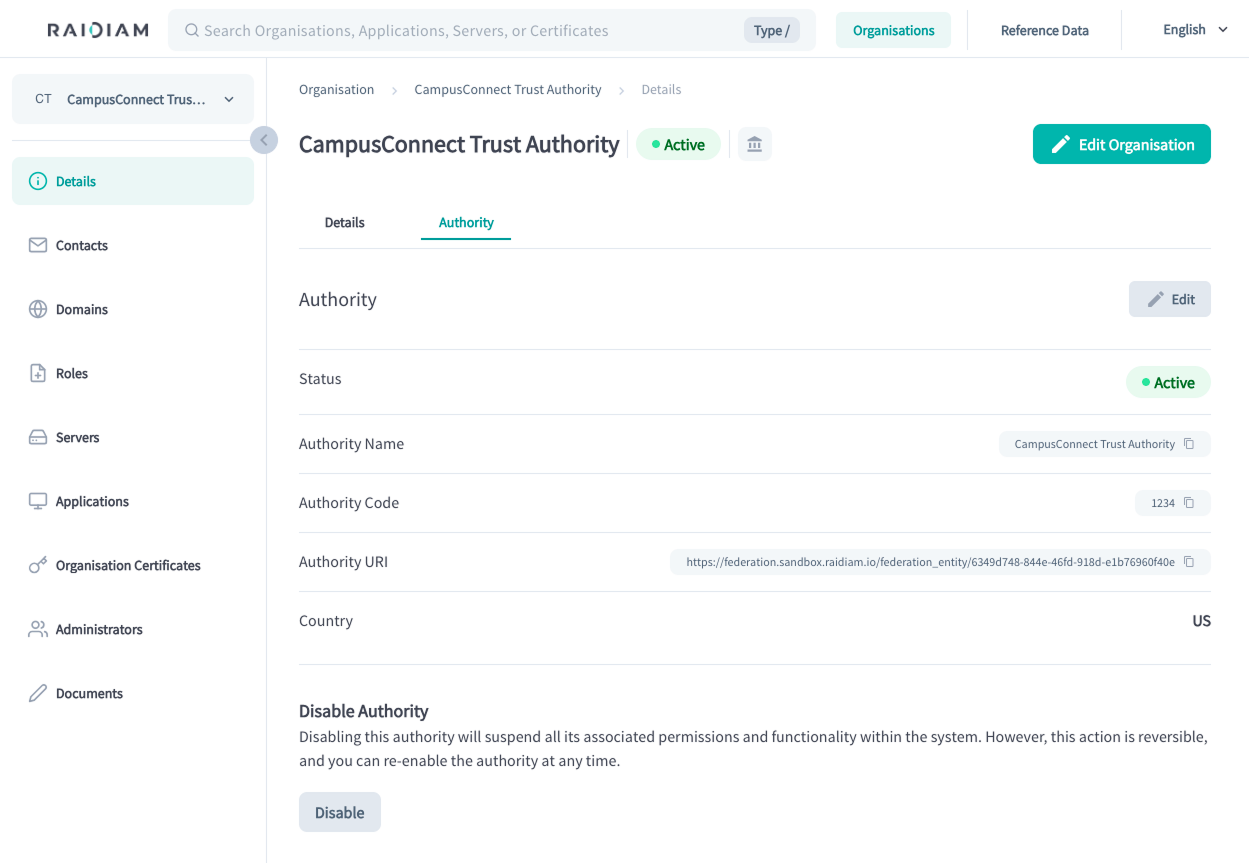
Authorities may either be the organisation administering the Trust Framework or they may represent the roles and information issued by an external authority within the Connect platform.
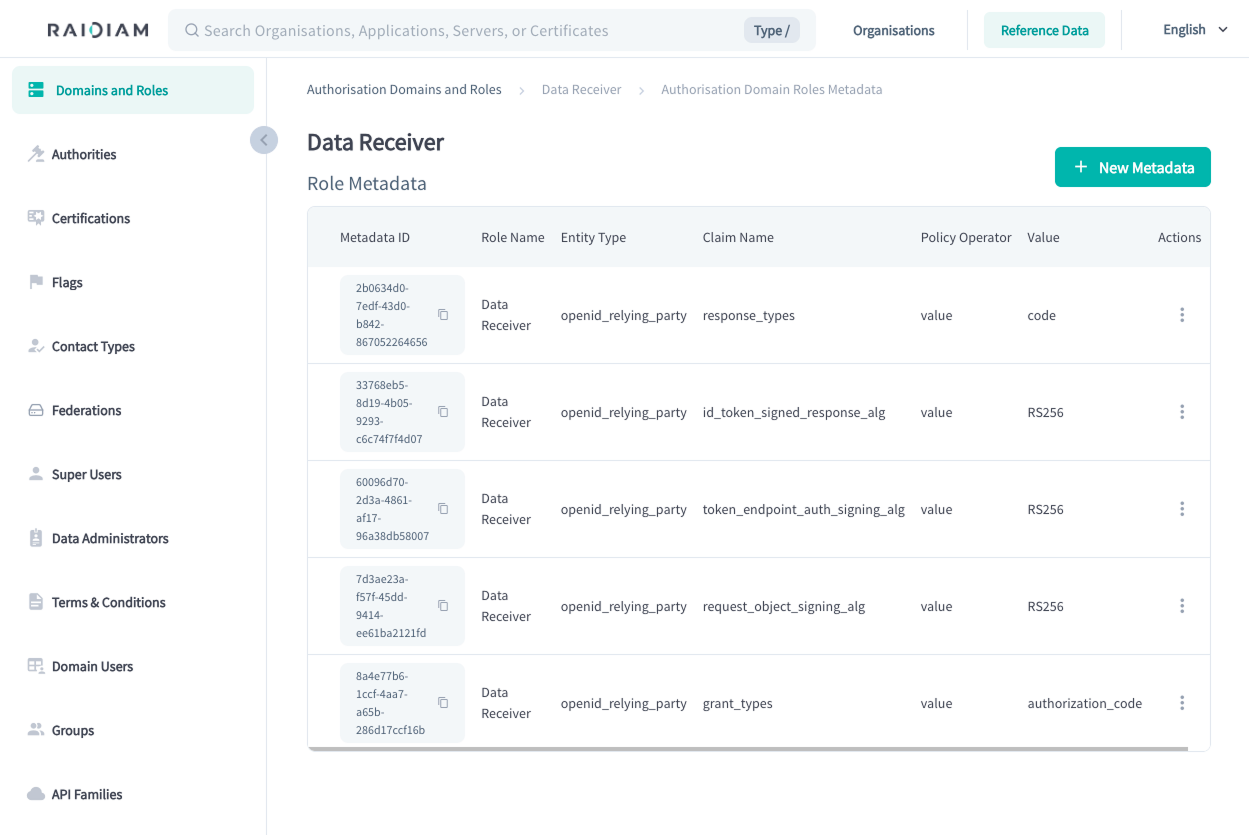
Federation operators control what metadata is issued for client applications and servers based on their role and domain context in the ecosystem. This enables governance-aligned metadata publication across participants while keeping federation operations centralized.
Trust chain operations
Participants can resolve and validate the trust chain to confirm trust relationships anchored in the federation authorities they have agreed to trust.
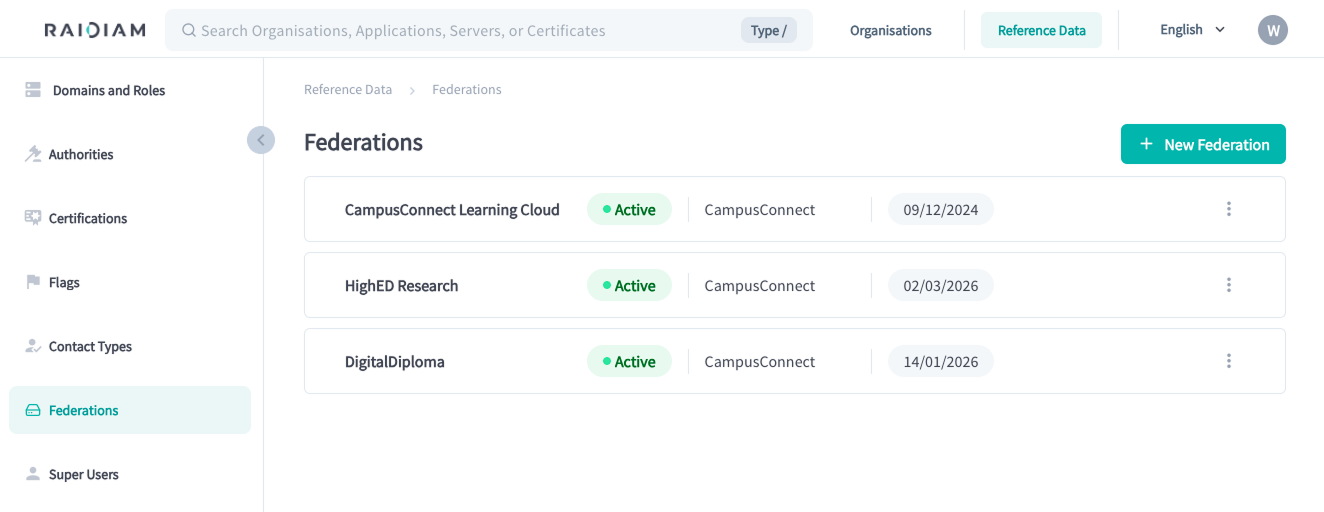
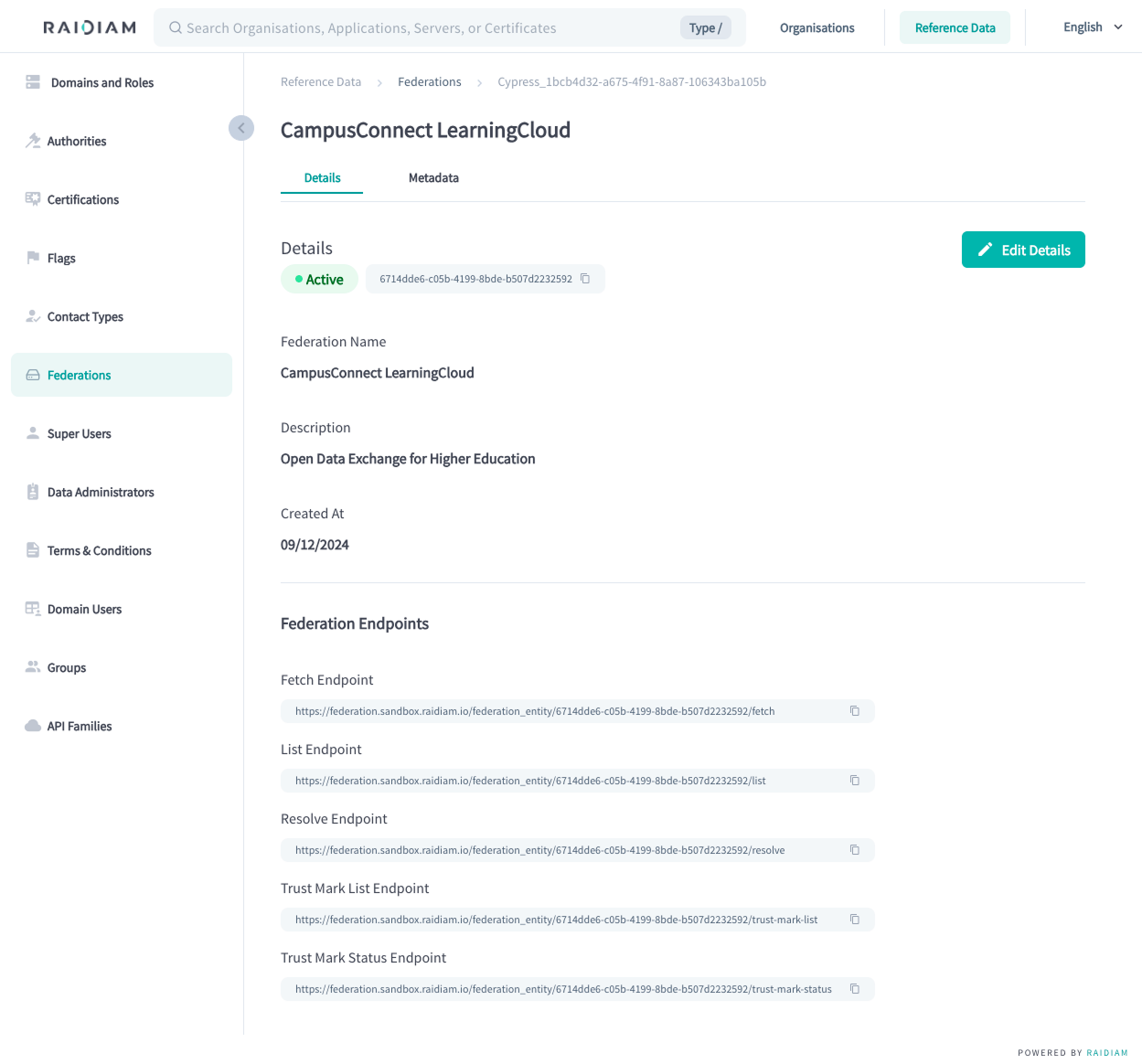
Federation endpoints
Raidiam Connect exposes the OpenID Federation endpoints required for trust operations, discovery, and metadata retrieval in deployed ecosystems.
What's next
-
Learn how trust chain validation works: Trust chain in OpenID Federation.
-
Understand key Federation entities and Federation policies.