OpenID Federation in the Education Sector: Governance and Trust
Higher education has been exchanging information across institutions “since forever” — certainly since the early days of the internet and research networking. What has changed is how dynamic these exchanges have become. Universities, research networks, ministries, and EdTech platforms now need to share data across borders, onboard new services efficiently, and meet rising expectations for privacy, security, and interoperability.
A second stage brought federation technologies like SAML, which made it practical to connect identity systems across organizations — but typically through bilateral relationships, manual onboarding, and static trust lists. That approach works for smaller communities, yet it becomes brittle when an ecosystem needs multilateral trust at scale.
OpenID Federation supports this next stage by providing a governed trust fabric for OAuth and OpenID Connect (OIDC), using cryptographically verifiable metadata, trust chains, and policy enforcement.
This article explains why OpenID Federation is a strong fit for the education sector, how it scales trust and discovery, and how it supports secure data exchange, wallets, verifiable credentials, and AI agent access.
Why OpenID Federation for higher education ecosystems
Higher education is inherently multilateral. A single research project might involve multiple universities, a national research network, a funding body, and a cloud provider. Student exchange programs require cross-border recognition of identities and academic records. New EdTech services need to integrate with campus systems without months of manual onboarding.
OpenID Federation enables these multilateral collaborations by allowing each organization and application to publish signed metadata and establish trust through a trust anchor and trust chain. This creates a shared governance layer that supports scale without forcing bilateral contracts between every pair of participants.
Traditional PKI and mTLS remain essential in high-assurance environments: they provide strong transport security and client authentication, plus operational primitives like key rotation, revocation, and lifecycle management. That is why PKI-based approaches are still recognized by high-assurance profiles such as HAIP. However, PKI and mTLS alone are not sufficient at ecosystem scale:
-
PKI and mTLS provide strong security properties, but they do not define how participants publish rich metadata, discover each other, or manage policy across organizational boundaries.
-
Manual certificate exchange and static allow lists become brittle as the ecosystem evolves.
-
Governance requirements such as accreditation, allowed roles, and policy constraints are hard to express and enforce with certificates alone.
OpenID Federation complements PKI by adding verifiable metadata, policy distribution, lifecycle automation, and automated client registration, which are essential for education ecosystems that grow over time.
Discovery, metadata, and scalable trust for education
In already existing education federations, discovery and onboarding often become a recurring pain point at scale. Many ecosystems rely on SAML-era patterns such as central metadata files, bespoke directories, and IdP discovery services (the classic “Where are you from?” screen). To make that usable, operators add SAML proxies and hub services that hide complexity — but they also concentrate operational risk, create brittle integration points, and make it hard to express ecosystem-wide policy beyond basic connectivity. OpenID Federation addresses this by making discovery and metadata distribution cryptographically verifiable and governed.
OpenID Federation introduces signed Entity Statements and Entity Configurations that allow participants to publish metadata in a standard, verifiable way. Trust is established through a trust chain that links a participant to a shared trust anchor, enabling automatic trust resolution without direct pre-registration. See the OpenID Federation overview and trust chain details for the core mechanics.
Another practical detail is identification: federation entities use globally
unique identifiers (the entity_id), expressed as https URLs. That
URL-based identifier scheme makes it easier to avoid namespace collisions across
institutions and supports decentralized hosting of metadata while remaining
linkable and verifiable through the trust chain.
Why this matters for education:
-
Discovery scales: applications can discover trusted identity providers, APIs, or credential issuers through federation metadata rather than manual onboarding.
-
Metadata is authoritative: endpoints, keys, and policy requirements are cryptographically signed and governed.
-
Trust registries become dynamic: instead of static lists, the ecosystem can rely on federation governance to publish and update who is trusted and under what rules. This aligns with the concept of a trust registry and the practical patterns described in Trust registries in scalable digital trust.
OpenID Federation is defined by the OpenID Foundation specification, which formalizes entity metadata, trust chains, and federation endpoints for discovery and resolution. See the OpenID Federation 1.0 specification for the full standard.
Secure data exchange with OpenID Federation + DPoP or X.509
Education data sharing often involves sensitive records: enrollment status, research datasets, student identity attributes, or accreditation information. Federation does not replace cryptography — it governs it.
Federation + DPoP
DPoP (RFC 9449) provides sender-constrained access tokens, binding tokens to a client-held key. This is particularly valuable for modern education apps and mobile clients where mTLS is impractical. In a federated ecosystem:
-
The client’s DPoP key and metadata are governed through the federation.
-
Authorization servers can apply federation policy to require DPoP for specific classes of clients.
-
Resource servers validate both the access token and the DPoP proof, while federation metadata ensures the client is accredited.
See the DPoP specification for protocol details.
Federation + X.509/mTLS
Many education and research networks already rely on mTLS for strong client authentication. OpenID Federation complements this by standardizing discovery and metadata publication (via federation endpoints).
Importantly, these models are not mutually exclusive. The same ecosystem can support both Federation + DPoP and Federation + mTLS in parallel, depending on the client type and risk profile. For example, mobile apps might use DPoP, while institutional system-to-system integrations keep mTLS.
From an implementation perspective, it is useful to treat this as a supported choice rather than a forced migration: education ecosystems can roll out federation for discovery and governance while enabling either DPoP or mTLS based on what each participant can operationalize.
Using keys bound to X.509 certificates can provide stronger security guarantees in some deployments (for example, by anchoring the client identity in a managed certificate lifecycle). Combined with federation governance, this remains a high-assurance pattern even after an ecosystem adopts federation.
In practice, client registration is often the scaling pain point in ecosystems that are not built on PKI-based onboarding. Many rely on OAuth 2.0 Dynamic Client Registration (DCR) as the default way to onboard partners and manage client metadata. This can work well for smaller communities, but at ecosystem scale it becomes difficult to govern consistently, keep metadata up to date, and avoid a growing backlog of manual exceptions.
OpenID Federation helps by providing two standardized client registration modes:
automatic registration (where the AS can register a trusted client on first
use based on federation metadata and trust chains) and explicit registration
(where a client is onboarded via a federation registration endpoint). An
Authorization Server can advertise which modes it supports in
client_registration_types_supported (see Enabling partner client registration).
-
Certificates can be managed and rotated through a governed trust anchor.
-
Federation policies can constrain allowed cryptographic algorithms and certificate profiles.
-
Trust resolution remains dynamic as new institutions and services join.
This is especially relevant for ecosystems currently built on PKI trust schemes; see Trust schemes and Strengthening API onboarding with trust and mTLS.
Verifiable credentials, wallets, and digital diplomas
Students increasingly expect to receive digital diplomas, transcripts, and micro-credentials in their wallets — ready to present when applying for jobs, visas, or further studies. This shift requires a Trust Registry of who is allowed to issue academic credentials, what are the attested and certified wallets, and more.
Verifiable credentials follow the W3C data model, where issuers sign credentials, holders store them in wallets, and verifiers validate them. See the W3C Verifiable Credentials Data Model for the standard. In some ecosystems, credential issuers may be identified by a decentralized identifier (DID); in that case, a DID can be stored as an alternative entity identifier as part of the issuer’s metadata — see Hybrid ecosystems combining OpenID Federation with decentralized identifiers (DIDs).
OpenID Federation fits this model by acting as a governed trust registry of issuers:
-
Universities, accreditation bodies, and ministries become federation entities with signed metadata.
-
The federation trust anchor enforces who can issue which credential types.
-
Wallets and verifiers can discover issuers and validate their status automatically.
This pattern aligns with education wallet initiatives and with the OpenID for Verifiable Credential Issuance ecosystem. For practical steps, see Getting started with wallet ecosystems.
AI agents in education and trust
AI agents are already present in education — from research assistants that summarize papers to tutoring systems that generate content or handle administrative tasks. Institutions need to control which agents can access which data and under what authority.
The key challenge is that agents often cross institutional trust boundaries: a research assistant may call APIs at multiple universities, a tutoring platform may integrate with several campus systems, and a vendor-managed agent may act on behalf of different departments. OpenID Federation provides a governed trust fabric to accredit these agents as clients across organizations, so institutions can separate experimentation from production and audit which agents accessed sensitive data.
Accrediting agent identity
Agents can be registered as federation entities with signed metadata that declares ownership, cryptographic keys, and operational endpoints. This establishes a verifiable identity for each agent, even when it is acting on behalf of a department or external vendor.
Linking agents to their home organization
Federation metadata allows a university or ministry to declare which agents it operates, and which external agents it recognizes. That linkage lets relying systems enforce which agent is permitted to access student records, research data, or administrative workflows.
Enforcing policy for agent access
Federation policies can require stronger authentication methods, constrain token profiles, or limit which agent types can access specific services. This is the same trust pattern explored in Building access control for agentic AI with OpenID Federation, adapted to education workflows where governance and accreditation are non-negotiable.
Migration path from legacy PKI/mTLS
Most education ecosystems already have PKI roots, SAML-based bi-lateral federations, and/or static trust lists. OpenID Federation does not require a single, disruptive migration. A staged migration is realistic and safe:
Start with a metadata overlay
Publish federation metadata for existing identity providers, authorization servers, and APIs. This creates a trust layer without changing how certificates or endpoints work today.
Register existing institutions as federation entities
Introduce federation entities for universities, research networks, and service providers while keeping existing certificates and mTLS policies in place. This lets teams validate trust chains while continuing to rely on their current PKI controls.
Move discovery and policy into the federation layer
As an organization joins a federation and confidence grows, applications can discover trusted endpoints via federation metadata rather than static directories. Over time, policy and key management can be centralized through federation governance, enabling automated rotation and consistent security enforcement.
This approach preserves operational stability while enabling long-term automation and scalability.
What a federated education ecosystem looks like
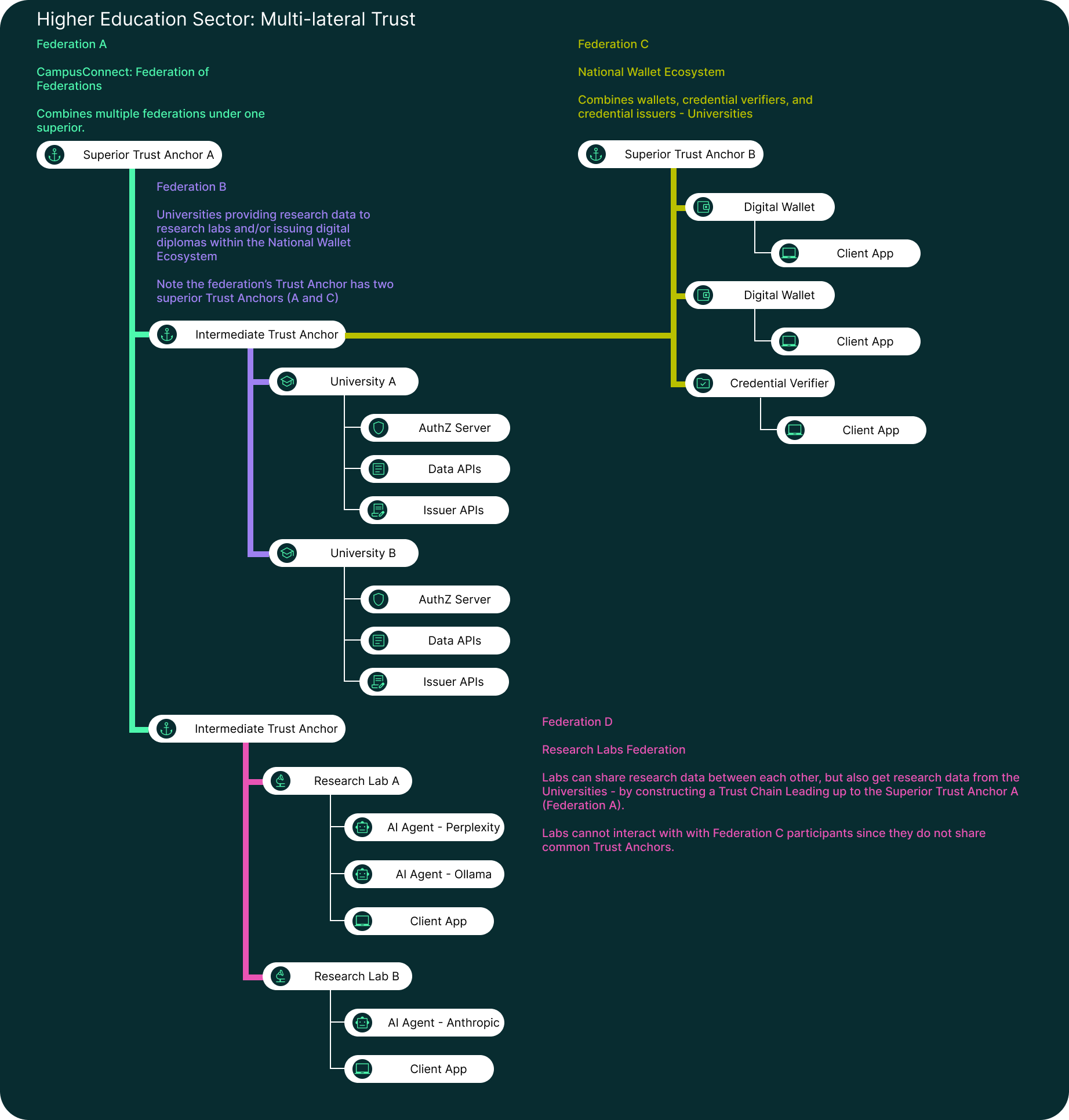
In practice, a federated education ecosystem mirrors the governance model that already exists across national education systems, research networks, and accreditation bodies. OpenID Federation turns that real-world structure into machine-readable trust relationships.
Trust anchors and intermediates
A ministry or national research network typically acts as the trust anchor, delegating authority to regional networks or accreditation bodies. Those intermediates publish policy and metadata that reflect their local governance rules while remaining anchored to the national framework.
Universities and EdTech platforms
Universities and colleges offer their education and research data as federation entities, while EdTech platforms register as relying parties with governed scopes. This supports cross-institution collaboration without requiring every integration to be negotiated and maintained bilaterally.
Wallet ecosystems alongside education and research federations
Wallet ecosystems are often governed nationally (or regionally) and may have a different trust anchor, policy, and assurance requirements than an education- and research-focused federation. Universities participating in an education and research federation (or a federation of federations) can still participate in a national wallet federation in parallel.
In practice, this means the same institution can issue credentials within the wallet federation while using the education/research federation for API access, and cross-institution service discovery. Wallet providers and verifiers can then discover trusted issuers through the wallet federation’s governance, enabling verification of digital diplomas and transcripts.
This model supports cross-border recognition of degrees, secure research collaboration, and future-ready digital identity services with governance at the core.
Conclusion
OpenID Federation gives the education sector a scalable trust framework that bridges governance and automation. It enables multilateral collaboration, dynamic discovery, governed data exchange, and trusted credential ecosystems — while supporting modern security mechanisms like DPoP and mTLS.
Ready to design a governed education trust framework? Explore Raidiam’s OpenID Federation concepts to see how trust chains, metadata, and policy can be applied to higher education ecosystems and Request Sandbox Access to see Federation in action.